Tech
What’s the use of Through-Hole Technology in PCB Designing?
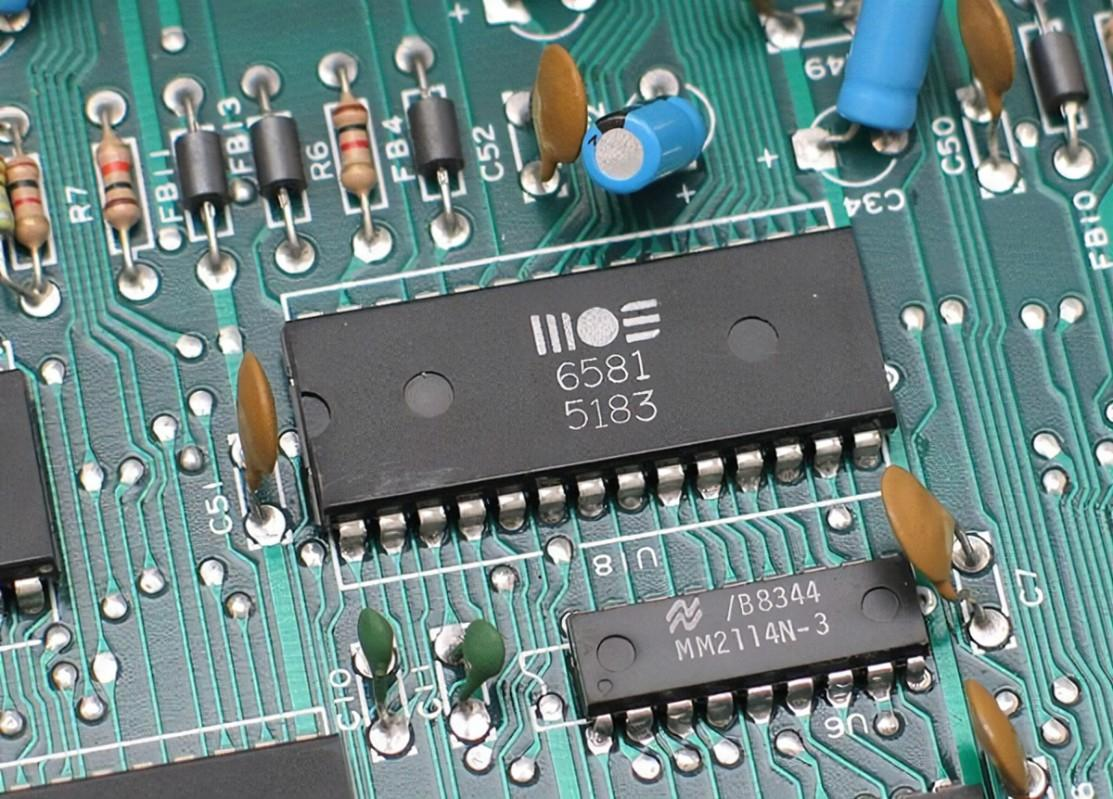
Greetings and welcome to today’s lecture. It is going to be a very interesting and interactive class about introduction to Through Hole Technology (THT) and Surface Mount Technology (SMT) that are applied in the process of designing the printed circuit boards. A PCB board is made up of properly designed circuits that are composed of connecting wires/paths and various electrical components. The electrical components are mounted on the board. In fact, they are fixed to the board. If the components are not fixed, then there will be no durability and this might lead to various losses that can be avoided. In the process of mounting these components, here is where the through-hole technology and the surface mount technology come in. They are very important processes in the design of printed circuit boards.
Overview.
This is one of the methods used in the attachment of components to PCB during the manufacturing process.
- THT is the oldest among these PCB attachment methods.
- For so long time it was the standard method that was used in the PCB assembly process.
- In the 1980s, when the surface mount technology process was introduced in the field of the PCB assembly, so many people thought that the THT method will become extinct but that is not the case.
- THT is used in all kinds of PCB designs i.e. Single Layer PCB, Multilayer PCB, Flexible PCB etc.
Through-Hole Technology (THT) is the method used in the attachment of the PCB electrical components and elements in the PCB whereby the components being placed have long leads that are soldered into the board through the holes drilled.
Process
- Dill holes on the PCB following the clients’ design.
- Select your components. They must have long leads. Also, remember components are on the design you have been given by the client.
- Place the components on the board and ensure that their leads are on the holes as defined in the design.
- Check that the components are in the positions described in the design to ensure that there will be no errors at the end of the process.
- Solder the terminals on the board accordingly. Ensure that the solder is on one side of the leads.
- Fill the other unsoldered side with flax.
Initially, this process was done manually hence it took a lot of time before coming up with a single complete board. Today, due to the changes in technology, it has become so easy to carry out the through-hole technology process. There are several automatic systems that aid out in the process and make it easy for the manufacturers, for example, the introduction of the automated insertion machines which actually helps in inserting the electrical elements into the drilled holes in the PCB before the soldering process starts.
Classifications of Through Hole Components.
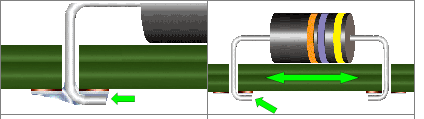
We have talked about the electrical components being placed on the PCB boards through the through-hole. These components can be classified into two that is the radial leads components and the axial lead components.
The radial leads components.
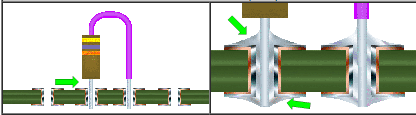
From the image displayed, there is already something that is building up in your mind. Observe it well. Look at the leads. Can you see something common with the device leads? Yes of course. You are right! Both the two leads originate from the common side of the components. That is what we call a radial lead component. This method finds its application commonly in the packaging of the capacitors.
The components can be mounted either vertically or horizontally.
Let us have a look at that from the images below.
The vertical mounting of the Radial THT components.
on this method, the component is always place perpendicular to the board while the base is placed parallel to the board. complete joint. Soldering is done on one side of the terminal and the other side is filled with flax.
The horizontal mounting of the Radial THT components.
the contact body is fixed on the horizontal as you can see from the images. The leads exhibit a very nice bend and also spacing. This allows the proper filling of the solder on the component hence forming the strongest
The Axial leads Components.
- These are the most commonly used elements of the THT PCB methods components assembly.
- Here the leads of the components appear from opposite sides to each other. See what is in the attached image on the left.
Also, it can be classified as horizontal mounting and vertical mounting.
horizontal axial mounting method
Vertical axial mounting method.
Applications of the THT
- High voltage areas eg in the medical equipment.
- High mechanical stress devices eg military equipment.
- High power areas eg in the steam boilers.
- High temperatures operating devices eg in the nuclear plants.
- Prototyping and testing of components.
Advantages of using the THT method of PCB components Mounting.
- The use of the THT method will ensure that you have a very strong mechanical bond compared to the SMTs components.
- THT bound components have high resistance to wear and tear and this is made possible by the use of the large soldering deposits at the terminals.
- The THT components are very easy to swap and repair the components hence they are the best for prototyping works.
- It is best suited for places where strong mechanical applications are needed such as aerospace and military equipment.
Disadvantages of the THT method of PCB components Mounting.
- Due to the drilling of the required holes, the production cost goes higher compared to the other method.
- Also, drilling of the holes requires some additional time, hence the THT method takes a longer time compared to other methods.
- This method limits the available routing paths for the multilayer PCBs because the drilled holes have to go through the given layers.
- The technology being used in the industrial mass production of the THT types of the PCB is less reliable compared to the other methods used.
The Difference Between THT and The SMT in PCB.
| THROUGH HOLE | SURFACE MOUNT |
| The components require the drilling of the holes for mounting. | No holes are required for mounting. Mounting is done through pads. |
| All the components are mounted on one side of the board and it is in most cases done manually. | Components can be mounted on either side of the board and the process is mostly automated. |
| The process of mounting is either manual or can be automated. | The mounting process is basically automated. |
| Do not employ the use of stencils. | This process involves the use of stencils to be achieved. |
| There are no vias in the pads. | Use of the vias in the pads. |
| These are used when a low density of the component is needed. | This works so well when the component density is very high. |
| Reworking and repairing are very simple. | Here the process of repairing and reworking is very complex. |
Tech
A Deep Dive into IP Transit Pricing Models and Billing Structures

Various aspects, such as bandwidth usage and provider agreements, determine the price of IP transit. Scalable pricing schemes are required to meet the requirements of companies. Standard pricing schemes include burstable, usage-based and flat-rate billing. Flat-rate pricing is appropriate for business houses with many customers because it provides uniform spending. Burstable billing provides you with flexibility in the event of an unforeseen traffic spike. Usage-based billing is billed on the volume of data that is used. Network performance and expense are influenced by service level agreements (SLAs). More dependable transit businesses are more expensive for uptime guarantees. Depending on the volume of data, some providers provide tiered pricing. Peering arrangements and traffic routing influence prices as well. Wholesale customers get discounts for big bandwidth commitments. Pricing transparency is required for firms to effectively manage network costs. To ensure stability, minimum bandwidth commitments can be incorporated in contracts. Firms can reduce costs by having a proper understanding of various models. A well-structured contract avoids surprise outlays. A pricing model needs to be chosen after a firm has examined its needs.
How IP Transit Pricing Adapts to Growing Business Bandwidth Needs
Scalable network solutions are required by businesses as bandwidth requirements increase. IP transit pricing need to factor in changing traffic patterns. Flexible plans are offered by providers to suit businesses with growing requirements. Bandwidth-intensive applications need more data transfer. Cloud computing and remote working use more bandwidth. Scalable pricing allows efficient cost control for businesses. Burstable billing is offered by some providers for short bursts. Flat rates are most appropriate for firms with steady traffic. Global organizations require high-bandwidth transit solutions. Periodic data exchanges conserve through payer contracts. Lower expenses are achieved through larger bandwidth commitments. Tiered approaches allow companies to choose the right plans. Providers look to identify usage patterns in order to design best-in-class solutions. Organizations can weather traffic spikes with scaling. Dynamic pricing models scale dynamically to regular demand. Future bandwidth growth is being supported by an experienced transit provider.
The Connection Between IP Transit Pricing and Network Redundancy
Redundancy in the network is necessary to ensure dependability and uptime. The IP transit pricing allows for the price of redundant infrastructure. Duplicate links are necessary to avoid outages for companies. Redundant routes increase network failure resistance. Several transit providers add to the reliability of the connections. Transit cost rises with increased redundancy levels. Failover functionality is included in the price of some providers. Companies that have critical applications invest in premium-level redundancy. Geographic diversification makes it less likely to fail locally. Redundant links minimize the interruptions caused by fibre cuts. Load balancing keeps traffic evenly distributed across multiple links. Peering agreements provide backup data paths for stability. Dedicated failover bandwidth is a standard part of pricing packages. Companies trade off redundancy investment against the cost of downtime. Mission-critical services require high availability solutions within the network. Disaster recovery plans will impact buying transit. SLAs establish recompense mechanisms for service down time. Up time is most important when negotiating a transit contract for companies. Good redundancy planning will balance cost against reliability.
Why IP Transit Pricing Varies by Region and ProviderGeographical position has an influence on the IP transit pricing. The cost of data transmission is influenced by regional infrastructure. Transit is cheap where the networks are large. Rural areas have the cost higher due to inefficient infrastructure. Global data routes influence price variations. Transit prices from different countries are determined by regulatory policies. Prices are competitive with the providers that have huge peering agreements. Transit costs are cheaper in competition-intensive markets. Prices are more expensive in monopoly-controlled networks. Regional pricing schemes are influenced by the locations of data centres. Cross-border links increase the expense of transit. Tiered pricing models are provided by providers in high-demand markets. Bandwidth cost and availability are determined by government policies. Transit is more expensive in developing markets due to infrastructure investments. The effectiveness of transit pricing is also influenced by access points of exchange. Certain localities offer subsidization to mitigate the expense of internet service. Transit cost maximization is supplemented by knowledge about these elements.
Tech
The Power of TWstalker: Tracking and Analyzing Twitter Engagement

Twitter remains one of the most influential social media platforms for individuals, businesses, and brands. With its real-time nature, the platform provides an unparalleled opportunity to connect with audiences, share ideas, and build brand presence. However, with millions of tweets being posted daily, tracking engagement and analyzing performance can be challenging. This is where TWstalker comes into play. TWstalker is a powerful tool that enables users to monitor Twitter activity, analyze engagement metrics, and gain insights into trending topics.
Understanding TWstalker
TWstalker is an advanced Twitter analytics tool designed to track and analyze Twitter profiles and engagement. It helps users keep an eye on their own activity and competitors’ performances, making it an essential resource for social media managers, digital marketers, and influencers. By leveraging TWstalker, users can monitor their growth, identify trending content, and optimize their Twitter strategies.
Key Features of TWstalker
- Profile Monitoring – TWstalker enables users to track any public Twitter profile. It provides a detailed overview of followers, tweet history, and engagement rates.
- Engagement Analysis – The tool examines likes, retweets, comments, and other interactions to determine which content performs best.
- Trending Topics and Hashtag Tracking – Users can identify trending hashtags and topics relevant to their niche, helping them tailor content for maximum engagement.
- Competitor Analysis – TWstalker allows users to monitor competitors’ Twitter activities, helping them understand industry trends and effective engagement tactics.
- Real-Time Updates – The platform provides real-time insights into Twitter activity, allowing users to adjust their strategies instantly.
- Follower Insights – Users can gain a deeper understanding of their audience by analyzing demographics, interests, and engagement behavior.
- Sentiment Analysis – TWstalker can gauge public sentiment around tweets, brands, or topics, helping businesses refine their messaging strategies.
- Historical Data Access – The tool offers historical engagement data, allowing users to analyze trends and measure long-term performance.
How TWstalker Enhances Twitter Engagement
1. Helps Identify High-Performing Content With TWstalker, users can analyze which tweets receive the highest engagement. By studying successful tweets, users can identify patterns such as content type, tone, hashtags, and posting times that work best.
2. Assists in Competitor Benchmarking Understanding competitors’ Twitter strategies provides valuable insights into industry trends. TWstalker allows users to compare engagement metrics with competitors, revealing what works and what doesn’t in their niche.
3. Improves Hashtag Strategy Hashtags play a crucial role in Twitter engagement. TWstalker helps users track trending hashtags and analyze their impact, ensuring they use the most effective tags to maximize reach and engagement.
4. Strengthens Audience Understanding Knowing your audience is essential for engagement. TWstalker provides demographic insights, such as location, interests, and engagement behavior, helping users tailor their content to resonate with their followers.
5. Optimizes Posting Schedule Timing is everything on Twitter. TWstalker analyzes engagement patterns to determine the best times to post, ensuring tweets receive maximum visibility and interaction.
6. Enables Real-Time Engagement Adjustments With real-time tracking, users can quickly respond to trends, engage with audiences at peak times, and make instant changes to their content strategy.
TWstalker for Businesses and Influencers
Businesses and influencers can leverage TWstalker to maximize their Twitter marketing strategies. Here’s how:
For Businesses:
- Monitor brand mentions and customer feedback.
- Track competitor campaigns and engagement levels.
- Analyze customer sentiment and tailor marketing messages accordingly.
- Identify brand advocates and potential influencers for collaborations.
For Influencers:
- Understand audience preferences and tailor content for higher engagement.
- Identify collaboration opportunities by tracking industry trends.
- Measure the effectiveness of different types of tweets.
- Engage effectively with followers based on data-driven insights.
Best Practices for Using TWstalker
- Set Clear Goals – Whether tracking competitor activity or increasing engagement, having clear objectives will help maximize TWstalker’s benefits.
- Monitor Consistently – Regular analysis allows users to stay updated on trends and make timely adjustments.
- Engage Actively – Data is valuable only when acted upon. Users should interact with followers, reply to comments, and share relevant content.
- Analyze Sentiment Trends – Understanding audience sentiment helps in crafting the right messages and avoiding potential PR issues.
- Leverage Historical Data – Looking at past engagement trends helps in long-term strategy planning.
Future of TWstalker and Twitter Analytics
With the growing importance of data-driven marketing, Twitter analytics tools like TWstalker will continue to evolve. Features like AI-driven predictive analytics, deeper sentiment analysis, and enhanced automation are expected to become integral to such platforms.
Businesses and individuals who invest in Twitter analytics will gain a competitive advantage by making informed decisions based on real-time data. Whether it’s optimizing tweets, engaging with followers, or tracking brand performance, tools like TWstalker will remain invaluable in maximizing Twitter’s potential.
Final Thoughts
TWstalker is an essential tool for anyone looking to maximize their Twitter engagement. By tracking key metrics, analyzing competitor strategies, and identifying trends, users can refine their approach and achieve better results on the platform. As social media continues to evolve, leveraging analytics tools will be critical for maintaining a strong online presence. Whether you’re a business, influencer, or casual Twitter user, TWstalker provides the insights needed to optimize engagement and make the most of Twitter’s vast opportunities.
Tech
Mastering PDF Management with Sejda: Features and Tips

Managing PDFs efficiently is essential for professionals, students, and businesses that rely on document workflows. Sejda is a powerful PDF management tool that provides a wide range of features to edit, convert, merge, and secure PDFs. Whether you are handling reports, contracts, or academic papers, Sejda simplifies the process with its user-friendly interface and cloud-based accessibility. In this guide, we explore the features of Sejda and provide expert tips to maximize its capabilities.
Understanding Sejda: An Overview
Sejda is an online and desktop PDF tool designed to help users manage their PDF files efficiently. Unlike many other PDF editors, Sejda offers a clean and intuitive interface, making it accessible even for beginners. With a strong focus on privacy, Sejda ensures that uploaded files are automatically deleted after processing, which is particularly useful for handling sensitive documents.
The platform supports a variety of operations, including merging, splitting, compressing, editing, and converting PDFs. It is available in both a free and paid version, with premium features tailored for advanced users and businesses. Sejda is compatible with Windows, Mac, and Linux, making it a versatile solution for different operating systems.
Key Features of Sejda
- PDF Editing
- Modify text and images directly within a PDF
- Add annotations, highlights, and comments
- Insert or remove pages from a document
- Whiteout text and redact sensitive information
- PDF Conversion
- Convert PDF to Word, Excel, PowerPoint, and other formats
- Transform images (JPG, PNG) into PDFs
- Convert scanned PDFs into editable text using OCR (Optical Character Recognition)
- Merging and Splitting PDFs
- Combine multiple PDFs into a single document
- Split a PDF into separate files based on pages or bookmarks
- Extract specific pages from a PDF
- Compressing PDFs
- Reduce file size while maintaining quality
- Choose different compression levels for optimization
- Compress images within a PDF to minimize storage requirements
- Security and Encryption
- Add password protection to sensitive documents
- Encrypt PDFs to restrict unauthorized access
- Digitally sign documents for authentication
- Batch Processing
- Perform bulk actions on multiple files at once
- Merge, split, or compress multiple PDFs in one go
- Automate repetitive tasks to save time
- Forms and Annotations
- Fill out and sign PDF forms electronically
- Add checkboxes, dropdowns, and text fields
- Highlight important sections for review
- Cloud Integration
- Import and export files from Google Drive, Dropbox, and OneDrive
- Work on PDFs directly from the cloud
- Sync edits across multiple devices seamlessly
Tips for Maximizing Sejda’s Potential
- Use Keyboard Shortcuts for Faster Editing Sejda supports various keyboard shortcuts to speed up the editing process. Learning these shortcuts can improve efficiency, especially when handling large documents.
- Optimize File Size for Easy Sharing If you need to send PDFs via email or upload them online, use the compression feature to reduce the file size without compromising quality.
- Leverage OCR for Scanned Documents When working with scanned documents, enable the OCR feature to convert images into searchable and editable text, making it easier to extract information.
- Automate Tasks with Batch Processing Save time by processing multiple files at once. This is particularly useful for businesses handling contracts, invoices, or large reports.
- Secure Sensitive Information Before sharing confidential PDFs, use the password protection and encryption features to prevent unauthorized access.
- Utilize Cloud Storage for Accessibility By linking Sejda with cloud storage services, you can access and edit your PDFs from anywhere, ensuring seamless collaboration and document management.
- Edit PDFs Without Downloading Software If you need quick edits, use Sejda’s web-based platform instead of downloading the desktop version. This is ideal for users who work on multiple devices.
- Customize PDF Merging Options When merging files, arrange them in the desired order and remove unnecessary pages before finalizing the document.
- Experiment with Different Output Formats If your document needs reformatting, test different conversion options to find the best output format that suits your needs.
- Take Advantage of the Free Version for Basic Needs Sejda’s free version offers essential features that can handle simple PDF tasks without requiring a subscription. Use it for occasional edits before considering a premium plan.
Why Choose Sejda Over Other PDF Tools?
- Affordable Pricing
- Sejda offers competitive pricing compared to Adobe Acrobat and other premium PDF editors.
- Flexible plans include daily, monthly, and yearly options.
- Privacy-Focused
- Automatically deletes uploaded files after a few hours.
- No risk of permanent cloud storage without user consent.
- User-Friendly Interface
- Designed for both beginners and professionals.
- Simple navigation and well-organized tools.
- Cross-Platform Compatibility
- Available on Windows, Mac, Linux, and web browsers.
- Works seamlessly across different devices.
- No Installation Required for Online Use
- Edit and manage PDFs directly in a web browser.
- Eliminates the need for software downloads.
Final Thoughts
Sejda is an excellent PDF management tool for individuals and businesses looking for an efficient, affordable, and secure way to handle documents. With its extensive features, including editing, conversion, security, and batch processing, Sejda streamlines document workflows while ensuring ease of use. By leveraging the tips mentioned above, users can maximize Sejda’s potential and enhance their productivity when dealing with PDFs.

 Business5 years ago
Business5 years agoFind out how useful a loan is without a credit check

 Digital Marketing5 years ago
Digital Marketing5 years agoIs YouTube Marketing Capable of Taking Your Business to the Next Level?

 Food4 years ago
Food4 years ago5 Best and Worst Foods for Boosting Metabolism

 Business4 years ago
Business4 years agoContent Creation Tips Every Digital Manager Needs to Know

 Business4 years ago
Business4 years agoBest Workplace Upgrade

 Lifestyle4 years ago
Lifestyle4 years agoHow to Choose the Best Air Fryer for Me

 Fashion4 years ago
Fashion4 years ago8 Top Leather Jacket Picks To Try Out This Year

 Tech5 years ago
Tech5 years agoFood Lion Employee Login at ws4.delhaize.com – MyHR4U