Business
7 Steps How International Shipping Works
The booming e-commerce across the globe has been seamlessly interconnected through the revolutionary forces of globalization, like never before. Businesses are expanding at an unprecedented rate in the international arena, given the easy accessibility of the internet and the evolution of digital currency.
The logistics and shipping industry has a significant role in aiding e-commerce businesses to increase their audience reach overseas, by providing a robust cross-border supply chain mechanism via different modes. As more and more e-commerce companies are willing to target a global consumer base, the importance of global shipping service providers rises.
As per Statista, the size of the international market for shipping containers was estimated at USD 6.41 billion in 2020 and is anticipated to increase at a CAGR of 12.0% from 2020 to 2028. Due to an increase in trade agreements between countries, the industry is expanding rapidly due to increased maritime shipping.
Understanding International Shipping
International shipping is the process of importing and exporting goods from one country to another. This can be done via air, land, or sea. It usually involves customs and immigration procedures as well. Depending on what is being shipped, there may also be special regulations that need to be followed.
When shipping internationally, it is important to be aware of the regulations and restrictions of the countries involved. Each country has its own rules and regulations regarding what can and cannot be shipped across its borders. It is the responsibility of the sender to make sure that all items being shipped comply with these regulations. Failure to do so can result in delays, fines, or even seizure of the goods by customs officials.
In international shipping, it’s important to choose a reputable and experienced company that can handle all of the necessary paperwork and logistics. The last thing you want is for your shipment to get held up in customs or lost in transit!
Various Elements Of International Shipping
There are many different elements to international shipping, and each one plays an important role in ensuring that goods arrive safely and on time. Here is a look at some of the most important elements of international shipping:
Customs clearance: This is the process of getting authorization from customs officials to import or export goods. It can be a complex and time-consuming process, but it is essential for ensuring that goods can move freely across borders.
Documentation: There is a lot of paperwork that goes into international shipping, and it is important to make sure that all of the documents are in order before shipment. This includes things like commercial invoices, packing lists, and other export documents.
Freight forwarding: This is the process of arranging for the transportation of goods from one country to another. Freight forwarders are experts in international shipping, and they can help to make sure that goods are shipped safely and on time.
Insurance: Shipping insurance is essential for protecting against loss or damage during transit. It is important to make sure that goods are properly insured before they are shipped.
Tracking: Tracking systems are used to keep track of goods as they move through the shipping process. This helps to ensure that goods arrive at their destination on time and in good condition.
How Does International Shipping Work?
Below are the points which explain the stepwise process of international shipping:
1. Export haulage
Export haulage generally refers to the transport of goods from one country to another. This can be done via various means of transportation, including air, land, and sea. Export haulage is a critical component of international trade, as it allows businesses to move their products to markets around the world.
2. Origin handling
Origin handling includes the handling of cargo from the time it is received at the warehouse until it is loaded onto a ship or aircraft. There are numerous parties engaged in this process, but it is the freight forwarder’s duty to coordinate these actions to ensure a smooth transition until the ship is loaded.
3. Export customs clearance
The importance of export customs clearance cannot be overstated. In order to ensure the smooth and legal flow of goods across international borders, it is essential that all shipments are properly cleared by customs. This process can be complex and time-consuming, but it is absolutely essential to ensuring compliance with regulations and avoiding penalties.
4. Transportation
Transportation plays a vital role in international shipping. It is responsible for moving goods from one country to another and for facilitating trade between nations. Without efficient transportation, international trade would be greatly hindered.
5. Import custom clearance
Import custom clearance is a crucial step in the shipping procedure since you need to make sure your cargo complies with the regulations of the nation you are entering customs.
6. Destination handling
All cargo handling tasks carried out in the destination warehouse are referred to as destination handling. Additionally, it entails cargo unloading and preparation for consignee collection. The staff of the destination port will take the cargo during this operation.
7. Import Haulage
The final stage of international shipping is import haulage. The delivery agent will now deliver the cargo to the specified address. Usually, the shipper or the receiver will make arrangements with a nearby transportation business to finish this task.
Things To Keep In Mind Before Shipping Internationally
1. Check the international shipping policies of the online store or company from which you are planning to make a purchase. Most online stores have their own set of rules and regulations regarding international shipping, so it is important that you are aware of these before making a purchase.
2. Choose a reliable and reputable shipping company. There are many shipping companies that offer international shipping services, so choose one that has a good track record and is known for providing reliable and efficient service.
3. Choose a shipping method that is best suited for the items you are shipping.
4. Make sure to include all required documentation with your shipment. This includes a list of items being shipped, as well as any special instructions that may be required.
5. Be prepared to pay any customs or duty fees that may be associated with your shipment. These fees vary depending on the destination country, so make sure to check with the shipping company or online store.
Conclusion
The future of international shipping looks bright, despite the challenges that the industry currently faces. The e-commerce boom has spurred demand for efficient and reliable international shipping services, and new technologies are making it easier and more cost-effective to ship goods around the world.
Another trend that is shaping the future of international shipping is the increasing use of drones and other unmanned vehicles for delivery. This technology is still in its early stages, but it has the potential to revolutionize the shipping industry by making deliveries faster, cheaper, and more efficient.
There are many opportunities for companies that are willing to invest in new technologies and innovations for going global with their businesses, and this will definitely require reliable logistics service partners who have the potential to provide end-to-end shipping solutions with an extensive supply chain network, such as NimbusPost. The shipping aggregator has carved its niche for offering flawless international shipping services to e-commerce merchants, SMEs, large-scale enterprises, and D2C brands across 196+ countries.
Business
How Businesses Utilize Custom-Printed Balloons To Stand Out At Events

There’s always plenty to see at events, all carrying different messages, brands, and graphics. Businesses seek effective yet cost-efficient methods of getting noticed at neighborhood fairs, trade events, product launches, and shop openings – custom printed balloons offer one such simple yet effective means – when utilized wisely, they help companies get noticed more effectively, create lasting memories more naturally, while strengthening their identity without seeming forced or faked out.
Visual Impact For Quick Visual Results
First impressions matter at events where attendees must quickly make choices about where and who to visit, such as launches of personalized balloons at events. Balloons printed with your design add height, color, and movement right away, while being easy to see in dense environments due to being larger and catching people’s eyes from all directions in a room.
Companies can turn balloon decorations into promotional tools by printing logos, slogans, or campaign messaging directly on balloons. These graphics draw people’s attention naturally, whether hung over a booth or framing an entrance – without needing to be actively promoted!
How Brand Identity Is Shaped Through Design
Brand consistency is at the center of successful branding efforts, so companies may use custom balloons to integrate their brand identity into an event environment through familiar colors, typefaces, and messages that people recognize from previous experiences with them. When used alongside banners, table coverings, or brochures for increased professionalism.
Consistency in visuals helps people recall your brand. Repeated exposure of logo or message throughout an event – even for just short time frames – has the ability to leave lasting memories with participants that build relationships between attendees. Over time, these reminders help strengthen mutual understanding among attendees.
Promote Interaction And Engagement
Not being noticed at events alone isn’t enough; engagement must also happen between attendees. Balloons inherently make people engage, particularly at locations that stimulate mobility and exploration; many visitors often stop for photos, questions, or free balloons at these events.
Businesses often utilize custom printed balloons at events to encourage participation from attendees and expand the brand message beyond the event, reaching people both physically and on social media, by giving attendees balloons as souvenirs of an experience or product demonstrations. When attendees take balloons home with them from these activities and carry the brand message out into the region and beyond social media, more people receive information from this brand message about its existence than would normally come through at just a one-day conference event itself.
Help With Affordable Event Marketing
Balloons can be an inexpensive and impactful way to promote any message or event, especially since their cost per impact can be so minimal. Balloons are easy to produce in large volumes at little expense; transportable; quick to set up; making them appealing solutions for firms attending many events with limited marketing resources or attending many similar occasions.
Balloons can make any room pop with color. By taking advantage of the balloon’s eye-catching nature, even small quantities may drastically transform its aesthetics, enabling businesses to spend their budget more wisely while creating an eye-catching presence that still gets people talking and involved.
Acclimatizing To Various Events And Situations
One of the greatest things about custom printed balloons is their versatility – they work for many events and businesses alike! Companies use balloons at conferences, networking events, grand openings, and sales events; stores use them during grand openings; nonprofit organizations can utilize balloons as fundraising devices, while community groups make use of balloons to raise money and spread awareness for their cause.
Make the balloon designs reflect the occasion: bright colors and eye-catching messages might work well at festivals and family reunions; more muted hues with less branding can work for professional settings or meetings. By accommodating to different events’ moods and settings, balloons remain interesting to a wide range of people.
Use Balloons In Your Plan
Balloons work great when integrated into an overall event marketing plan, which should include clear messages, courteous personnel interactions, and strong calls-to-action. Businesses that excel are those that carefully consider where things will be put while matching designs to the goals of an event.
Businesses often enlist skilled promotional partners such as Perfect Imprints to ensure that the balloon designs meet brand guidelines and event goals, thus turning a simple item into an effective marketing tool.
Final Thoughts
To stand out in competitive event venues, companies need to use visual elements creatively and with purposeful intent. Custom-printed balloons offer companies an effective means of drawing attention without overcomplicating their approach – when used strategically, they provide unforgettable memories and will stay with people long after an event has concluded.
Business
Understanding Your Rights in a Building Dispute

Construction disputes are generally tense and complex for homeowners builders contractors. Your awareness of your rights in the event of a dispute is essential to effective settlement of the dispute. Delays substandard work contract breaches or payment problems are all possible elements of such disputes. Confidence to deal effectively with the problems can be gained through acquaintance with the legal construct of construction contracts. Misunderstanding or vague words of a contract usually cause disputes that can bring in confusion to the two parties. Protection of your interests entails your knowledge of your own legal responsibilities and rights as a builder or a homeowner.
When Should You Hire a Building Disputes Solicitor?
Seeking legal advice at an early stage is important in the case of a construction dispute. If a dispute with a contractor or homeowner gets out of hand beyond simple miscommunication legal guidance may be necessary. Your rights will be protected and your case will be dealt with properly if you instruct a solicitor. A building disputes solicitor can provide you with the tools you require to proceed with your dispute by clearly establishing your rights and responsibilities under the contract. They can help you decide if the most appropriate action is arbitration mediation or litigation. By helping to resolve the conflict amicably their intervention may sometimes prevent it from escalating.
How Solicitors Help Resolve Disputes Over Variations and Change Orders
Change orders and variation clauses are standard in construction contracts and they sometimes result in conflict. Because of unforeseen occurrences or changing requirements during the project these clauses authorize changes to the original scope of work. However there could be conflicts regarding the scope of the changes or associated costs. A building disputes solicitor can prove to be extremely useful in such circumstances with regards to understanding the conditions of the contract. They will help establish if the prescribed procedures for authorizing variations have been complied with and if the variation orders are within the contract terms. In a bid to reflect changes precisely solicitors also help in preparing addenda or contract amendments. For additional work they can verify the billing to ensure that it is fair and according to the contract.
By obtaining legal counsel both sides can avoid misunderstandings and miscommunications that may lead to long and costly court cases. In some instances lawyers may suggest mediation or negotiation as other dispute resolution methods which can lead to faster and more cost-effective settlements. If a settlement is not possible in more serious cases the attorney can prepare for litigation and represent your interests in court.
Dealing with Owner-Builder Disputes: What Legal Protections Apply?
While dealing with owner-builder disputes is sometimes challenging it is very important to know your legal rights. Owner-builders are obligated by law in most jurisdictions to comply with specific insurance and licensing regulations which act to protect both parties in future disputes. If issues arise such as construction defects delays or payment disputes the owner or contractor can seek recourse under consumer protection or contract law. Owner-builders generally must provide guarantees in relation to the materials and workmanship for a set period as per the law. It is often recommended that mediation or arbitration be considered prior to going to court if the dispute cannot be resolved through friendly settlement. By getting the services of a lawyer at the earliest you can make sure that you comply with correct procedures and avoid costly mistakes by having your rights and duties explained. With the correct documents like signed agreements variation orders and letters you can increase the chances of a lawsuit victory. Owner-builder disputes can be resolved ultimately faster fairly and with less hassle if you know your rights and have professional guidance.
Business
Unlocking Growth: Essential Strategies for Small Business Success

In the fast-paced realm of entrepreneurship, small businesses face both thrilling opportunities and formidable challenges on the path to growth. The journey from fledgling startup to thriving enterprise is fraught with pivotal decisions that can spell success or failure. With market dynamics in perpetual motion, how does one ensure a business not only survives but thrives? The secret lies in unlocking the right strategies that cater to scalability, financial robustness, and market adaptability. This article delves into the essential considerations small business owners must keep in mind to steer their ventures toward sustained growth and success.
Growing Pains or Gains Ensuring Scalability Without Compromising Quality
As a small business owner, envisioning growth is exciting, but it also comes with its own set of challenges. One critical aspect to address is scalability. Can your business model expand without sacrificing quality or customer satisfaction? By focusing on scalability, you can streamline operations and optimize processes, achieving economies of scale that lower costs per unit as your business grows. This means enjoying higher profit margins without compromising the value delivered to your customers. Efficient resource allocation is key, ensuring that time, money, and manpower are directed towards essential tasks. This flexibility allows your business to remain responsive to market changes, setting the stage for long-term success.
Financial Foundations Crafting a Blueprint for Business Growth
Funding your growth initiatives requires a solid financial strategy. It’s crucial to develop a comprehensive financial plan that includes effective budgeting, meticulous cash flow management, and exploring diverse funding sources. By setting clear financial goals aligned with your strategic aims, such as market expansion or operational efficiency, you can ensure your budget is actionable. Implementing a robust cash flow monitoring system is vital to maintain liquidity and avoid financial shortfalls. Additionally, diversify your funding portfolio by exploring options like crowdfunding or angel investors. This multidimensional approach not only supports immediate growth opportunities but also builds resilience against financial uncertainties.
Brand Brilliance Enhancing Your Presence Through Strategic Marketing
To capture a wider audience, enhancing your brand identity and marketing strategy is essential. As we move into 2025, integrating trends like artificial intelligence, short-form videos, and sustainable practices will redefine consumer engagement. Strengthening your brand involves creating a memorable experience that resonates with your target market. A data-driven approach allows you to personalize marketing efforts, increasing engagement and brand loyalty. By continuously refining your communication techniques and leveraging social proof, you can effectively highlight the unique benefits of your offerings and stand out in a competitive market.
Digital Dreams Realized Transforming Your Business for Growth
In today’s fast-paced market, digital transformation is crucial for small businesses aiming to streamline operations and boost competitiveness. Embracing technologies such as cloud computing and advanced AI can scale your operations and enhance customer experiences by personalizing engagement and improving efficiency. Digital initiatives can significantly uplift customer satisfaction and loyalty, driving higher revenue and market share. Integrating digital strategies isn’t just an option for survival; it’s a pathway to thriving in an increasingly competitive landscape.
Building a Dream Team Enhancing Talent Retention Through Culture
Cultivating an organizational culture that attracts and retains top talent is essential for business growth. This involves fostering effective team dynamics where open communication, learning opportunities, and diversity are prioritized. A competitive workplace environment is crucial, as many employers struggle with employee retention and attracting new talent. By establishing an appealing employee value proposition, you can significantly reduce turnover costs. Creating a supportive and inclusive atmosphere not only enhances employee satisfaction but also drives long-term business success.
Insight-Driven Triumphs Harnessing Market Insights for Strategic Growth
Thriving in a competitive marketplace requires thorough market research and competitive analysis. Understanding emerging trends allows you to identify new opportunities and potential threats that impact your business growth. Evaluating competitors’ offerings and customer feedback provides a clear comparative landscape. Regularly assessing your strengths and weaknesses using SWOT analysis ensures adaptability to market changes. These insights inform strategic decisions, helping you create innovative strategies that propel your business forward.
Efficient Invoicing for Seamless Expansion
A consistent and simple invoicing system is essential for expanding your small business efficiently. By using an online invoice builder, you can generate professional invoices that reflect your brand identity, including your logo and company colors. Setting precise payment terms and issuing invoices promptly enhances your cash flow management, ensuring timely payments. Offering various payment options caters to diverse customer preferences, reducing barriers to payment and fostering stronger client relationships. Embracing customizable invoice templates allows you to save time and effort, ultimately freeing up resources to focus on strategic growth initiatives.
The road to small business growth is far from linear; it’s a dynamic journey filled with evolving challenges and opportunities. As you navigate this ever-changing landscape, remember that success hinges on adaptability, resilience, and strategic foresight. By embracing scalable operations, crafting robust financial plans, and leveraging modern marketing and digital tools, you align your business with the demands of tomorrow’s market. Moreover, fostering an organizational culture that prioritizes talent retention and capitalizing on market insights can propel your venture forward. The canvas of small business is vast, painted with the vibrant hues of innovation and perseverance. Let these considerations guide your brush strokes as you create a masterpiece of sustainable growth and enduring success.

 Business5 years ago
Business5 years agoFind out how useful a loan is without a credit check

 Digital Marketing5 years ago
Digital Marketing5 years agoIs YouTube Marketing Capable of Taking Your Business to the Next Level?

 Food4 years ago
Food4 years ago5 Best and Worst Foods for Boosting Metabolism

 Business4 years ago
Business4 years agoContent Creation Tips Every Digital Manager Needs to Know

 Business4 years ago
Business4 years agoBest Workplace Upgrade

 Lifestyle4 years ago
Lifestyle4 years agoHow to Choose the Best Air Fryer for Me

 Fashion4 years ago
Fashion4 years ago8 Top Leather Jacket Picks To Try Out This Year

 Tech5 years ago
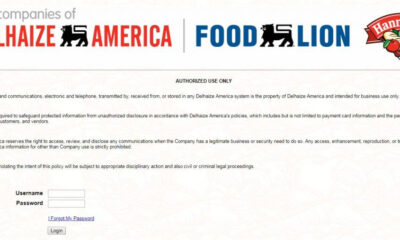
Tech5 years agoFood Lion Employee Login at ws4.delhaize.com – MyHR4U